Anti-aliasing
Also: Myles is my conceptual device.
One of the reasons I've always thought that OpenID never caught on is simply because not many people self-identify with URLs. Yet. Those of us who live and breath the web long ago understood the attraction (sometimes even the value) of having a personal domain and the benefits of being able to hang services (OpenID, for instance, or some other trust/validation mechanism) off of it. That is still by and large a level of technical engagement with the plumbing that many people may not be able to wrap their heads around. Even when they can, though, most people just don't have the time to care about it. Lots of things have a way of losing out to, say, children.
That's started to change in recent years as Facebook and Twitter, the twin towers of the Broadcast Nation, have insulated themselves in to everyone's lives and taught people to address others in conversation by their username or some service-level equivalent handle. Which is an interesting wrinkle in what will be possible in years to come simply because people are comfortable with the notional construct of an addressable online identity. I doubt that OpenID will ever be more than a good idea that happened too soon but something like it will probably gain a thold over time.
I mention all of that because Tom Coates and I had a long conversation about custom URLs (generally referred to as "path aliases") on Flickr and ultimately about the larger issue of conceptual devices like addressable identifiers. You know the part where you can get to my photos by visiting http://www.flickr.com/photos/straup instead of http://www.flickr.com/photos/35034348999@N01 (where 35034348999@N01
is a unique ID for my account and a hold-over from the original game that birthed Flickr). Specifically, we were talking about the inability of users to change their path alias once its been created. This is a situation that is further exaserbated or at least made more confusing by the ability of users to change their username (the name that Flickr uses to say "Hi So-and-so!" when you visit the homepage) as many times as they want.
So if you chose the path alias "bobby" when you created your Flickr account way back in the dawn before time known as 2005 but have decided that you'd really rather now be known as "robert" in online circles you are out of luck when it comes to your photos. This is one of those good news / bad news situations.
The good news is that Flickr has never and (if there is any justice in the world) will never break URLs. When you create a custom URL Flickr agrees to make sure that only your photos will appear at that URL. And even if you delete your Flickr account the site won't suddenly start showing someone else's photos when a person visits that address on the Internet.
The bad news is that Flickr never got around to making it possible to change your path alias in a way that preserved the old one and simply redirected visitors to the new URL. I don't honestly remember why we didn't do it during my time but it was probably the usual combination of having too few people doing too many things multiplied by it being a time before the Broadcast Nation had been adopted en masse (read: how many are really going to care enough to change their custom URL?) and it became a feature that kept being pushed down the stack.
If you ask me now, I think Flickr should make it possible for users to change their path aliases. It would involve a bit of planning and a bit of head-scratching to account for the massive big-iness of Flickr and all its users and to account for the edge cases but it's certainly possible.
As a way to work through some of the issues I added the ability to create and change path aliases to parallel-flickr. The code first checks a local list of path aliases but also checks Flickr for existing aliases since parallel-flickr is, by design, a very tiny subset of the entire user base. That still leaves open the possibility that a local (parallel-flickr) user might claim an alias that a Flickr user claims in the future. If that (Flickr) user then gets added to the (local) database who gets to use the alias in their URLs?
I opted to give it to the user who claimed it first (locally) because parallel-flickr is a personal backup and if someone's already claimed it that probably means they are an active user. The other user's photos are still addressable using their Flickr ID (or NSID
, the 35034348999@N01
I mentioned before.) Which means that the code needs to do some extra hoop-jumping to see if a path alias is shared between users and display some notice to that effect. Which means that the whole project starts to feel a lot like the maze of horrors that was (is) trying to merge Flickr and Yahoo! accounts but there you go. If you disable the path aliases can change feature in parallel-flickr all the localized magic stops and the site just chugs along as a mirror image of Flickr, which means the hypothetical shared path alias will belong to the same user who owns it on Flickr.
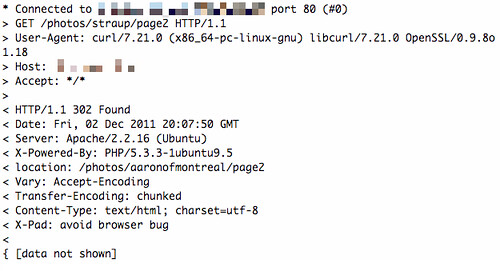
The place where Tom and I disagree about changing aliases is how to handle the redirects at both a network and a conceptual level. I was tempted to grossly misrepresent Tom's argument in order to bait him in to finally blogging again but I haven't and if I get it wrong it's because I got it wrong not because of something Tom said. At the network level there are two types of redirects identified by their numerical status codes. (There are actually several types of redirects but we're just going to leave them in the corner for now, as a practical matter.) Status code 301 says "the URL you are looking for is gone forever and the stuff that used to be there lives over here, at another URL". Status code 302 says "the URL you are looking for has temporarily moved over to this other URL".
Tom thinks Flickr should issue 301-style redirects for path aliases that have changed and I think Flickr should issue 302-style redirects (and ignore the temporary
part in the semantics of the status code). My argument for 302 redirects is simply that to do otherwise would violate the promise that Flickr makes that URLs don't change. Tom's argument is two-fold. First, that lots of things actually do change, or are impermanent, on the Internet and to pretend otherwise is simply ignoring reality. Second, by not allowing for path aliases (which are "usernames" by any other... name) to be recycled Flickr is further strip-mining the finite natural resouce known as "good" usernames and perpetuating the proliferation of awful usernames like bobby.1497
.
I am sympathetic with both arguments although I don't think the first holds weight when we're talking about photographs. I agree with Tom's basic premise that things online should be allowed to die, whether it's by the hand of the person who created them or just because it's probably healthier in the long run to remember that some things in life are transient. I just don't think that applies to photographs, especially photographs that exist on a photo sharing website where people are actively encouraged to share their pictures publicly. They are not the same flights of fancy that status messages, for example, are considered to be. There is the larger issue that if your business is built on the trafficing of things that are meant to be ephemeral then the value of your business itself (to users) is ultimately no less ephemeral. And before you say it, I don't actually believe that, in the end, people will think things like Twitter messages are any less important than photographs but that's a whole other story.
We are hard-wired for photos or more precisely still images (I've got six thousand years worth of claims that "painting is dead" to back up that outrageous claim, by the way) and they come with enough emotional baggage and social triggers that they deserve to be treated with care and thought. At the very least they deserve to be guaranteed some degree of permanence. This is one reason that parallel-flickr mirrors Flickr's URL structure. If the shit ever does hit the fan (I still don't know anything you don't, okay?) then all those Flickr links you've got lying around can at least be kept alive (or un-dead) by replacing "flickr.com" with "my-copy-of-parallel-flickr.com" which is not ideal but is better than nothing.
Tom's other argument is that by allowing users to change their path aliases without also putting old aliases back in to the pool of available names then eventually there just won't be any good names to choose from. On the face of it, this is true. We have twenty years of ugly and stupid usernames at AOL and then Hotmail and Yahoo! and now Google to point at. I would argue this is the function of bad, or at least lazy, UI design more than it is a proof of people's inability to think of a username they want to self-identify with. This is also a hard problem. It is one of those genuinely hard problems that no one has solved and I do not have a handy list of best practices for getting users to think about identity within the constraints of a seemingly finite set of possibilities. On the other hand we have entire languages at our disposal and entire histories of literature and poetry with which to encourage people to think about the act of naming things as something other than just "bob.jones.3327".
Not to mention a legacy of semi-anonymous communities of interest (often weird but usually not creepy) that have been role-playing and choosing names and guises for themselves to indicate that, really, it's a problem people are more than capable of solving. For example, I would totally create a Twitter account for NEWAESTHESTICHULK except for the part where Twitter names can only be 15 characters long...
What I am saying is that it's a problem we haven't ever really tried to solve at scale. There's a reason that everyone has been so eager to use services like Facebook and Twitter for managing user accounts because it means they can effectively punt on the problem entirely. That's all good so long as, in the long run, you understand that you are share-cropping your users and are comfortable with the realities that these companies will always have a knife to your throat. This is, after all, still business.
I sometimes use Twitter as an example not so much of opportunities missed but of opportunities for active encouragement passed by. From a business perspective you can't really fault Twitter for pursuing the Broadcast Nation strategy. It has served them fantastically well and without much coaxing from Twitter itself lots of people have figured out how to take the constraint of a message no longer than 140 characters and use it to make language sing and dance in new ways. There is a fine line between actively encouraging users down a certain path and being overly proscriptive and I could easily be convinced that Twitter badgering users to think about the art of crafting a message, of describing a moment, would just be annoying. Again, that's the hard part but life is short so why not take a stab at solving the difficult things?
But back to Flickr: If Flickr went down the road of allowing users to change their path alias then there is still a valid argument to be made that they should allow a user to willingly jettison a custom URL in to the void. To say: I know what I'm doing and I don't care if someone else's awful and disturbing (or just saccharine) photos show up in the place where my pictures used to live.
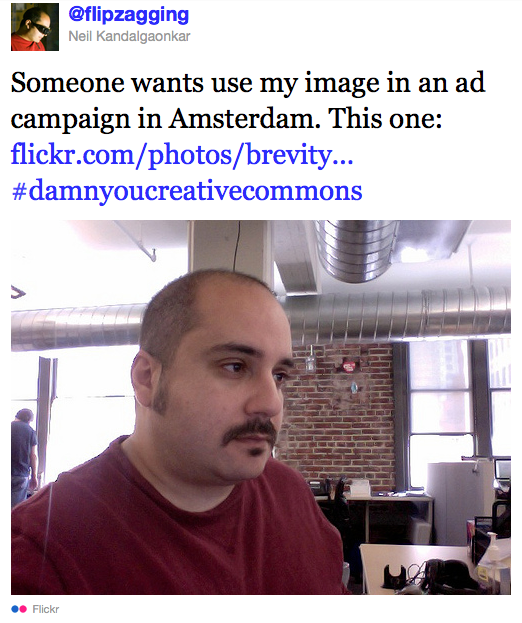
The only problem here is that it brings up another really hard design problem that no one has much bothered to tackle: How you convey to people that an action on their part is effectively crossing the point of no return. After the Flickr Commons launched lots of users wanted to be able to give their photos a public domain license (often confusing it with the no known copyright license that Commons photos are assigned which is not at all the same thing). Most people on the team, I think, were in favour of allowing users to say their photos were freely available in the public domain and it certainly wasn't a technical challenge.
We simply couldn't think of a way to really make people understand that once they'd done that there was absolutely nothing they could do to control how someone else used their photos. Nothing. Forever. Always. This was also around the same time that people were starting to discover the goofy-funny-not-really-flattering photos of themselves that they'd given a Creative Commons license because that's the right-and-good thing to do were suddenly being used in national ad campaigns and seeing themselves on posters plastered all over the place. This still happens today. To people who used to work at Flickr.
That's what I mean when I say that photos are quantifiably different.
So, I suppose you should be able to throw an old path alias back over the fence but it seems like a bit of a wasted effort to do so without also trying to crack some of the larger issues that shadow the reasons for doing it in the first place.
I've been thinking a lot about these kinds of conceptual devices, or constraints, and the opportunities they present to nudge and shift the discussion around a topic but it's all woolier than I'd like. I suppose that is their nature, to be fuzzy around the edges in a way that gives people enough of a rough guide to see that there's actually a path forward (rather than a wide open-ended landscape) but without erecting fences so high they block out the sky. It makes things difficult to talk about in concrete terms but it seems to me that this is how you at least try to get out from under the burden of all the common wisdom that's gotten us in to the messes like the one we struggle with around usernames and identity.
We did a lot of stuff wrong during my time at Flickr but if I had to highlight one thing we fucked up it was somehow creating an environment where people started to believe that their photos were not good enough for Flickr
. I mean, really, how did we ever let that happen? I was speechless the first time a friend said that me and for the record: It was never part of the plan. How did we ever let people think that there is one measure of photography? How did we let people imagine that a medium which gave the world both Ansel Adams and Garry Winogrand (a photographer who died with a reported 10, 000 rolls of undeveloped film in his studio and who said that every time you take a picture you are hopefully risking failure
) and everyone else in between was about any other than the joy and the discovery of the possible, fy equipment and technique and measures of "good"-iness be damned?
Since then, the Instagram steamroller has come along and earned its success fair and square by making a thing that is genuinely fun and easy and immediate to use. There's a lot about the larger project that I find problematic but you can not fault them their ability stripping away all the cruft at the intersection of photography and our Interphones. And all it took to get a whole crowd of people who I know and were intimidated (apparently) by Flickr (of all things) genuinely interested again in the act of photography was, let's be honest here, a heavy application of 1970's vaseline-porn filtering to their pictures.
Say what you want about those goofy filters (and I am the last person to call that particular kettle black) but they have been a startlingly good device for getting people to play at taking pictures again.
This blog post is full of links.
#anti-aliasingDwelling and Staring
This is another one of those epically long blog posts, and I barely even wrote any of it. It's also pretty fucking depressing. I think I'm going to go and get drunk and watch videos of kittens after I publish it or maybe just show up on Myles' doorstep and ask for a hug. What follows has largely been my day, for good or bad.
I've been reading P. W. Singer's Wired for War
and planning to do a dog-eared blog post, when I finished, alongside Matt Martin's Predator
(as in the one he pilots) which I read last month. Then this morning I started reading about United States v. Jones
which will decide whether or not GPS vehicle surveillance performed without a court order is a violation of the Fourth Amendment (since, you know, you drive around in public already) so I decided not to wait any longer
After the essay about the Supreme Court case I found myself reading about the investigation in to the sexual assault charges against Dominique Strauss-Kahn which I include here only because the weirdest part of the article is that a huge chunk of the reporting
was done by surveillance cameras and cell phone and electronic keycard log files. From there it seemed only natural to finally read the Washington Post's Top Secret America
series, end to end.
And by the time I'd gotten through all that Nate had sent along a piece the Post published yesterday on aerial drones in Gaza that might as well be part of Thomas Pynchon's Gravity's Rainbow
. Meanwhile, Iran is claiming to have not simply downed, but p0wned, an American stealth drone that looks as though it fell from Batman's utility belt. Good times.
I did also add the ability to filter your faves by photographer in parallel-flickr this morning, so I guess that's something...
Predator
by Matt Martin & Charles Strasser
- Call him a bonus. Truck and driver. Blue light special, Kmart shoppers. Two for the price of one.
- There had been a power outage in the satellite uplink in Europe. I had no further control of the plane. It automatically shut down its lasers and weapons and turned away from the target to fly a lost link profile.
- My radio crackled. “Roger that, Agony 31.”
- The driver slammed the trunk lid and looked all around. That was a dead giveaway for suspicious.
- and immediately transferred my video feed to marines on the ground so they could see what I was seeing.
- I held my breath when the Abrams thundered directly at the car and pointed its 120mm main cannon right at the driver through his windshield.
- The United States had just taken off the front of an old Toyota at the price of about sixty-eight thousand dollars. Eventually we might get a handle on the insurgency—if we didn’t go broke first.
- Marines tightened their seal on the city until it was as tight as a condom on a large cucumber.
- everybody knew it was over. That was made even plainer when teams of U.S. Army lawyers began arriving in the city with suitcases full of cash to award to people with damage claims. In effect, they were insurance claims adjusters.
- the MarcBot, about the size of a toy truck, had a video camera mounted on its tiny mast. It was the first ground robot to draw blood in Iraq after troops fighting in the streets of Baghdad and Fallujah discovered that they could jerry-rig a Claymore antipersonnel mine to it and send it snooping into a waiting ambush or into an alley or a building to blow up the bad guys.
- Yob and I posed for photos with the other GIs. It reminded me of the scene in Mars Attacks where Martians pose for cheesy snapshots in front of Mount Rushmore while other Martians blow it up.
- Battle damage assessment could be relayed so quickly that the original strike aircraft could reattack almost immediately if necessary.
- My speculation is that Statler had committed a classic error partly as a result of the poorly designed off-the-shelf interface that was the Predator cockpit.
- M0-M1-M2 instead of M1-M2-M3. One incorrect key to the left. Instead of turning on the engine cooling fan, the aircraft responded to the incorrect stimulus and engaged its autopilot. The next thing Statler knew, the Predator was attempting to fly to the next waypoint on its programmed route—even though it was on the ground.
- The history of warfare might be considered a history of missing the target while attempting to become more accurate.
- Today, a single Hellfire missile fired from an unmanned aircraft could do a job that would have required a hundred or more B-17 sorties during World War II.
- “If you don’t really give a toss,” Sharkey pointed out, “you can just put an autonomous weapon running into a crowd anywhere. It’s only a matter of time before that happens.”
- the unblinking eye of a remote presence and the rapid response capability of a kill chain that never quit.
- On my cue, Kimberly fired up her target marker and shot an infrared laser beam onto the street about ten meters in front of the QRF’s lead vehicle. Night vision goggles made the beam clearly visible to the Humvee driver. All he had to do was follow the beam.
- One guy was still alive, at least for the moment. I almost felt sorry for the poor bastard. All broken and bloody, he reached out one hand and clawed at the ground, trying to pull himself along. The other arm lay limp and twisted against his side. Nobody in the GCS uttered a word. We merely watched the video, mesmerized, both awed and horrified by the carnage and this guy’s dying effort.
- He was bound to screw up sooner or later, and one of us would get a P-Model chance at him.
- I had notified him of the situation; he liked to be present whenever we fired a shot.
- Sparrow refused to conduct the mission until discrepancies could be resolved. The point would have been rendered mute were the fighters using GPS-guided bombs. They could simply have plugged in the coordinates, and the smart bombs would have been on their way.
- War wasn’t fair, particularly in the new age of warfare. Anyone who thought it was hadn’t been there.
- What many of them failed to realize was how easily, barring legal niceties, these phones could be invaded by law enforcement and intelligence services.
- I experienced the by-now-familiar pixilation on the screen as the missile launched from its rail to briefly interrupt the return link.
- “The OIF [Operation Iraqi Freedom] fight has morphed into a conflict where all sensors are shooters and all shooters are sensors.”
- In an attempt to make better use of available pilots, the air force designed a prototype GCS called a multiaircraft control (MAC), which allowed a single pilot to fly more than one airplane at the same time.
- Everything went along fine as long as three of the four aircraft were only punching holes in the sky.
- Crews knew their areas, their targets, and the personalities behind the chat. More than at any other point in the war so far, they were closer to “fused” operations, in which intel and ops were conducted simultaneously.
- avoiding the prioritization problems of decentralized control through sheer numbers.
- A cockpit could be rolled onto an aircraft for a manned mission during phase I of a major contingency. Once air superiority was achieved, the cockpit could be rolled off and replaced with fuel for longer-duration unmanned sorties.
- In March 2009 the air force, working with Pentagon researchers, approved the development of a prototype of the next U.S. spy craft—a giant unmanned dirigible that could remain aloft for as long as ten years while flying at an altitude of sixty-five thousand feet, safe from enemy fighter planes and out of range of most missiles.
- As a pilot of the future now,
Wired for War
by P. W. Singer
- Thucydides, the founder of both the study of history as well as the science of international relations, described war as a punishment springing from man’s hubris. It is our arrogance chastised.
- while we accept change in other realms, we resist trying to research and understand change in the study of war.
- I am the kid who played with Transformers who now consults for the military.
- one story may be an anecdote, but a collection of them is data.
- The reason for this different approach is not simply to break the mold, or rather mould, of scholarly style or to give heart attacks to the old guard with my generation’s manner of thinking and writing, even on important issues like war. Rather, as much as we pointy-headed scholars hate to admit, this is how people process information most efficiently.
- iRobot recently launched a multimillion-dollar advertising campaign called “I Love Robots” that shows people talking about their robots and the work they do.
- Under an additional $20 million repair and spare parts contract, the company also operates a “robot hospital” in Baghdad.
- I noticed some scorched paper stuck to one of the bots. Edward Godere, a vice president at Foster-Miller, explained, “The soldiers have started taping Playboy centerfolds to the side of the robots.
- Foster-Miller’s Talon gets its night vision from simply slipping a soldier’s night vision goggles over the robot’s camera
- The navy wants to reduce the number of personnel on its ships because one fewer sailor on board saves $150,000 a year in operating costs.
- is remote-controlled from afar by either radio or a spooled-out fiber optic wire.
- At the time of my visit, Foster-Miller was exploring replacing the controller with a Nintendo Game Boy-style controller, hooked up to virtual reality goggles.
- The robot’s zoom lens not only extends the shooter’s sight, but matches it exactly to the weapon’s.
- Likewise, its battery allows it to be hidden somewhere in “sleep” mode for at least seven days and then wake up to shoot away at any foes.
- one observer even said it looked like “a flying meat fork.”
- The ugly little drone
- In other words, Global Hawk can fly from San Francisco, spend a day hunting for any terrorists in the entire state of Maine, and then fly back to the West Coast.
- The plane itself costs some $35 million, but the overall support system runs over $123 million each.
- Soldiers love it because they can now peer over the next hill or city block, as well as get their own spy planes to control, rather than having to beg for support from the higher-ups.
- Because they rarely see the Global Hawks, officers in the field joke that these pictures are mainly used to fill the PowerPoint briefings for the generals back in D.C.
- Its software was modified to target mortar shells and rockets instead of missiles, with the idea that it would essentially put up a wall of bullets to protect bases.
- The business of protecting buildings, borders, and airports and preparing to respond to disaster generates $30 billion a year and is projected to reach $35 billion by 2011. As one report on the homeland security industry put it, “Thank you, Osama bin Laden!”
- The drones are launched by radio control and then automatically fly a patrol pattern using GPS, staying at four hundred feet, just below what the government requires for certification. While in the air, they search out any illegal immigrants crossing the border and record the images to TiVo for playback and review.
- after Katrina, cell phone towers went out because of storm damage and a lack of power, which hampered both residents on the ground as well as rescue efforts. During the next disaster, the plan is to use a UAV as an “aerial cell tower.”
- Tesla would not be the last inventor to find out that what was technically possible mattered less than whether it was bureaucratically imaginable.
- The concept was that they would create extra targets, forcing the enemy to use up their ammunition on the unmanned planes, rather than shooting down American pilots.
- The secret to their success was a stratagem of first using UAVs to gather the electronic frequencies of the Syrian radars. Then a swarm of UAVs flew over the area, sending out fake signals. The Syrians, thinking it was the real attack, fired off their missiles. While they reloaded, a second wave of Israeli jets flew in and took out the entire defense system, using missiles that homed in on the radars that the drones had unmasked.
- It could maneuver so fast and hard that its pilots blacked out.”
- the difference between a computer and a robot is the former’s lack of effectors to change the world around it.
- The major problem is the ever-growing amount of data that robots send to the user. As artfully described in National Defense magazine, it is like “the TV episode of I Love Lucy where Lucy and Ethel are at the chocolate factory and the chocolate just gets out of control, and you never get back in gear.” An iRobot engineer confesses, “User interface is a big, big problem.”
- A defense industry rule of thumb is that “if it takes more than two clicks to get the information, you are wasting your time.”
- “Having a dedicated operator for each robot will not pass the common sense test.” If robots don’t get higher on the autonomy scale, they don’t yield any cost or manpower savings.
- Besides their ability to carry heavier weights, robots have one more fundamental difference. They come with their own power systems. This opens up new possibilities, as the robot can now power its own weapon. One example is called Metal Storm and has been tested out on iRobot’s Warrior. Metal Storm, originally invented by an Australian grocery store worker, is a gun that uses electricity rather than gunpowder to shoot out stacks of bullets. The switch from chemical to electric power allows it to fire far faster, as many as a million rounds per minute. Thus, instead of shooting at one target with one bullet, Metal Storm can do such things as deconstruct a target, by shredding it apart bullet by bullet, or put up an actual wall of bullets in the air to protect against incoming missiles. The makers also note that this electric machine gun is good for “crowd control.”
- The appeal of lasers lies not just in their flexibility, but also in the belief that they would have an immense psychological effect.
- The request went on to describe how the laser “can be compared to long range blow torches or precision flame throwers, with corresponding psychological advantages.”
- Yet in many ways, the form that a robot takes is most dependent on the effectors.
- As robotics writer Daniel Wilson describes, “Every vehicle is a robot waiting to happen.”
- It originally came out of a request by the special forces for robotic planes that could do such things as fly up to a windowsill and then creep inside.
- Such transforming robots do have a key vulnerability. Any opaque molecule can block the reformation and communication pathways. It would have made a far less exciting movie, but all that Sarah Connor needed to do to defeat the T-1000 Terminator was pour maple syrup on it.
- When Moore first wrote on the phenomenon in 1965, a single transistor cost roughly five dollars. By 2005, five dollars bought five million transistors.
- As more and more people bought such items as video and then digital cameras, it dropped the cost of equipping robots with the same kind of cameras (their electronic vision systems) by as much as 75 percent.
- Rodney Brooks at iRobot calls this kind of cross-transfer “riding someone else’s exponentials.”
- and a loudspeaker to warn any insurgents that resistance is futile.
- The next step is DARPA’s plan announced in 2007 for a “VULTURE” (Very-high-altitude, Ultra-endurance, Loitering Theater Unmanned Reconnaissance Element) drone, which the agency hopes will be able to stay aloft for as long as five years.
- Another problem is that flying the smaller designs actually makes most human operators nauseous. Imagine watching video from a TV camera mounted on a butterfly, as it bobs up and down crossing a room; that is the sensation of flying a micro-drone.
- A small satellite carrying humanoid robots will be blasted into the heavens. “Once safely in orbit, the satellite will release its robotic passengers, who will proceed to fight each other in the vacuum of space.”
- Wars are a human phenomenon, arising from human needs for human purposes. This makes intimate human participation at some level critical, or the entire exercise becomes pointless.
- and Casualty, where the system just did what it thought best to keep the ship from being hit.
- with an eye toward not merely precision, but fashion and aesthetics,
- All told, DARPA estimated that as much as $100 million in investment was spurred, as well as the equivalent of $155 million worth of free labor. One military robotics company executive joked that “the best part of the Grand Challenge is using the college kids like cheap slave labor.”
- While the military is the major funder of robotics research, much of it actually plays out in public view. We just aren’t watching.
- McKenna’s pimp hand is strong.
- Having robots painted black made them stand out as targets and the 140-degree heat in Iraq made them hard to even touch.
- This kind of back-and-forth between the people who design and make robots and the users in battle produces a pattern of almost continual improvement. For example, one navy robot, the Mk. 3 RONS, went through some thirty-five different changes in its first five years of operation.
- “I’m a guinea pig and that makes me more firmly resolved to prove that it’s possible.”
- “self-synchronize” their efforts.
- For those happy powers that set the technological pace, war will become an essentially frictionless engineering exercise.”
- “Sloppy thinking” was how retired marine Frank Hoffman described it. “Theories and business models drawn from the exuberance surrounding the IT revolution displaced quite a bit of history and factual context.”
- Rather than a seamless flow of information, soldiers wrestled with everything from Web browsers constantly crashing due to desert sand to heat fouling up equipment designed for use in offices, not battlefields. Indeed, at one point in Davis’s reporting, an army lieutenant resorts to navigating a convoy using an improvised GPS and some handheld walkie-talkie radios that he had bought from a hardware store back home. The soldier joked that “if we run out of batteries, this war is screwed.”
- With all the networking, the demand for the batteries turned out to be much higher than ever planned (the marines alone were using up 3,028 of them a day). But there were no stockpiles. Explains the DefenseTech journal, “Major combat missions during Gulf War II almost ground to a halt—because of a shortage of batteries.” The only reason that the plug wasn’t literally pulled on the Iraq invasion is that thirty other nations loaned the United States extra batteries.
- It transforms the very agent of war, rather than just its capabilities.
- Even with robots and other new unmanned technologies, war is still about using violence to make the other side do what you want.
- when the prototype of the automated DIVAD (division air defense) cannon was first tested in the 1980s. Instead of aiming at the target helicopter flying overhead, it mistakenly targeted a port-a-potty toilet behind a review stand full of visiting dignitaries (the toilet had a rotating fan in the vent, which led the gun system into thinking the potty was the target helicopter).
- Unfortunately, the jammers are just as lethal to the robots. The Raven drones, for example, are supposed to fly themselves home if they lose their signal, but reportedly sometimes just crash when they fly over a unit using jammers.
- In a U.S. Army journal article, Ralph Peters described how future wars would also include electronic “battles of conviction,” in which opposing combat systems struggle to “convince” each other’s electronics to do things their own side doesn’t want.
- Insurgents in Iraq have already resorted to digging “tiger traps,” deep holes for ground robots to roll over and fall into.
- War journalist Robert Young Pelton even jokes that the most effective counter against robots like the SWORDS may turn out to be a “six-year-old kid armed with a spray paint can.” As he explains, it would take a bloody-minded military indeed to program a robot to shoot an unarmed kindergartner. And yet all the kid has to do is spray some paint into the camera and the technologically advanced robotic system would be defeated.
- A linked problem of coordination is what is known as the “bandwidth battle.” Essentially, there is only so much space in the spectrum to convey all the instructions, commands, information, and requests going back and
- seemingly outdated but still effective
- to hide and sustain itself.
- “The use of force is but temporary. It may subdue for a moment, but does not remove the necessity of subduing again....A nation is not governed which is perpetually to be conquered.”
- Steven Metz, a professor at the Army War College and author of the book Perdition’s Gate: Insurgency in the 21st Century.
- They placed tiny “walls” of concrete and even garbage around the bomb, to keep the robot from getting close enough to reach the bomb with its arm. They began to place the bombs high off the ground.
- Lieutenant General David Barno, the former commander of U.S. forces in Afghanistan, described the Taliban’s strategy, “Americans have the watches, they have the time.”
- This ability to “dwell and stare,” as one Predator pilot described, means that the unit can get a sense of the area and “see things develop over time.”
- The advantage of UAVs is not merely the dwell time, and the accuracy of their sensors, but also that they create a backlog of events that can prove incredibly useful.
- the “Gotcha sensor,” an air force program to “provide persistent staring” at an area, where the system will automatically note any significant changes.
- For example, a mother submarine able to send out just a dozen tiny subs can search a grid the size of the entire Persian Gulf in just over a day.
- The U.S.S. Jimmy Carter, one of the navy’s Seawolf class subs, reportedly even has tiny robotic drones that can launch underwater and tap into “the under-sea fiber-optic cables that carry most of the world’s data.”
- one firm in Ohio has fitted out a propeller-powered C-130 cargo plane so that it can not only launch UAVs, but also recover them in the air. The drones fly in and out of the cargo bay in the back, turning the plane into an aircraft carrier that is actually airborne.
- all the boids needed to do to organize themselves together as a flock was for each individual boid to follow three simple rules: “1. Separation: Don’t get too close to any object, including other boids. 2. Alignment: Try to match the speed and direction of nearby boids. 3. Cohesion: Head for the perceived center of mass of the boids in your immediate neighborhood.”
- “We will see if not identical technologies, then parallel technologies being developed, particularly because of the off-the-shelf nature of this all. We’ve reached the point where the bad guys don’t need to develop it; instead they can just buy it.
Keeping Watch on the Detectives
by David Cole
- It requires the Court to decide whether the Fourth Amendment's safeguards remain meaningful in the digital age, when widely available technological innovations—including GPS devices, cell phones, computer data-mining programs, and the like—make it possible to watch citizens more intimately and comprehensively than was remotely conceivable when the Bill of Rights was adopted.
- If, as the Obama administration would have it, the state can engage in such monitoring without first developing any objective basis for suspicion, privacy may become as "quaint" and "obsolete" as then White House counsel Alberto Gonzales once characterized the Geneva Conventions.
- Now they just attach a GPS monitor to his vehicle and make sure it has long-lasting batteries. Because it is so inexpensive, and operates without human intervention, the GPS makes dragnet surveillance possible. How should Fourth Amendment doctrine respond?
- Because of the "third-party disclosure" rule, the Fourth Amendment at present provides no protection for that information.
- One Nation Under Surveillance , Simon Chesterman, a law professor at the National University of Singapore and New York University,
- Seventy percent of the US intelligence budget goes to private contractors,
- More fundamentally, if we give up on limiting collection, what is left of privacy?
- As Justice Breyer asked at oral argument in the Jones case, "What would a democratic society look like if a large number of people did think that the government was tracking their every movement over long periods of time?"
- He suggests that courts should not ask whether government access to an individual's web-browsing data, for example, invades a "reasonable expectation of privacy," but whether it "causes problems of reasonable significance," an intentionally expansive term designed to encompass, among other things, the potential for illegitimate targeting of government critics.
- The Fourth Amendment demands only that "searches and seizures" be reasonable, not that all government action be reasonable. Inviting the court to oversee all "problems of reasonable significance" is not a sufficiently precise, realistic, or persuasive alternative.
- A more nuanced approach, in my view, would retain the Court's focus on "reasonable expectations of privacy," but would recognize that privacy should encompass information that the government could not realistically obtain without resort to technological innovation that enables sweeping surveillance without human intervention—such
- The state, unlike Google, can deprive us of our liberty, and is more likely to punish dissent; sharing information with Google and with the government are therefore qualitatively distinct acts.
- little recourse other than simmering resentment.
- Time and again, constitutional law has bent to the imperatives of the state in conflict.
- In the Matter of an Application of the United States of America for an Order Authorizing the Release of Historical Cell-Site Information , Case No. 10-MC-897 (NGG) (E.D.N.Y. Aug. 22, 2011).
What Really Happend to Strauss-Kahn?
by Edward Jay Epstein
- Camera tage at the restaurant shows her crawling under the table.
- There, the two men high-five each other, clap their hands, and do what looks like an extraordinary dance of celebration that lasts for three minutes.
- What he did not know was that at 12:51, according to the records of the BlackBerry company, it had been somehow disabled.
- While DSK believed he had left it in the Sofitel, the records obtained from BlackBerry show that the missing phone's GPS circuitry was disabled at 12:51.
Top Secret America
by Dana Priest & William M. Arkin
- In all, at least 263 organizations have been created or reorganized as a response to 9/11. Each has required more people, and those people have required more administrative and logistic support: phone operators, secretaries, librarians, architects, carpenters, construction workers, air-conditioning mechanics and, because of where they work, even janitors with top-secret clearances.
- Every day, collection systems at the National Security Agency intercept and store 1.7 billion e-mails, phone calls and other types of communications. The NSA sorts a fraction of those into 70 separate databases.
- the new $1.8 billion National Geospatial-Intelligence Agency headquarters, which will be the fourth-largest federal building in the area and home to 8,500 employees.
- Every one of these buildings has at least one of these rooms, known as a SCIF, for sensitive compartmented information facility. Some are as small as a closet; others are four times the size of a tball field.
- SCIF size has become a measure of status in Top Secret America,
- Command centers, internal television networks, video walls, armored SUVs and personal security guards have also become the bling of national security.
- The problem with many intelligence reports, say officers who read them, is that they simply re-slice the same facts already in circulation. “It’s the soccer ball syndrome. Something happens, and they want to rush to cover it,”
- The overload of hourly, daily, weekly, monthly and annual reports is actually counterproductive, say people who receive them. Some policymakers and senior officials don’t dare delve into the backup clogging their computers. They rely instead on personal briefers, and those briefers usually rely on their own agency’s analysis, re-creating the very problem identified as a main cause of the failure to thwart the attacks: a lack of information-sharing.
- Another senior defense official recalls the day he tried to find out about a program in his budget, only to be rebuffed by a peer. “What do you mean you can’t tell me? I pay for the program,” he recalled saying in a heated exchange.
- “This is a terrible confession,” he said. “I can’t get a number on how many contractors work for the Office of the Secretary of Defense,” referring to the department’s civilian leadership.
- A 2008 study published by the Office of the Director of National Intelligence found that contractors made up 29 percent of the workforce in the intelligence agencies but cost the equivalent of 49 percent of their personnel budgets.
- “Could we keep this building running without contractors?” said the captain in charge of information technology. “No, I don’t think we could keep up with it.”
- For one, unlike in government, if an SGIS employee did a good job, he might walk into the parking lot one day and be surprised by co-workers clapping at his latest bonus: a leased, dark-blue Mercedes convertible. And he might say, as a video camera recorded him sliding into the soft leather driver’s seat, “Ahhhh … this is spectacular.” And then there was what happened to SGIS last month, when it did the one thing the federal government can never do. It sold itself.
- Such coziness worries other officials who believe the post-9/11 defense-intelligence-corporate relationship has become, as one senior military intelligence officer described it, a “self-licking ice cream cone.”
- The new gunmetal-colored office building is really a kind of hotel where businesses can rent eavesdrop-proof rooms.
- The existence of these clusters is so little known that most people don’t realize when they’re nearing the epicenter of Fort Meade’s, even when the GPS on their car dashboard suddenly begins giving incorrect directions, trapping the driver in a series of U-turns, because the government is jamming all nearby signals.
- From the road, it’s impossible to tell how large the NSA has become, even though its buildings occupy 6.3 million square feet - about the size of the Pentagon - and are surrounded by 112 acres of parking spaces.
- The schools, indeed, are among the best, and some are adopting a curriculum this fall that will teach students as young as 10 what kind of lifestyle it takes to get a security clearance and what kind of behavior would disqualify them.
- “I can spot them,” she says. The suit. The haircut. The demeanor. “They have a haunted look, like they’re afraid someone is going to ask them something about themselves.”
- On a recent night in Memphis, a patrol car rolled slowly through a parking lot in a run-down section of town. The military-grade infrared camera on its hood moved robotically from left to right, snapping digital images of one license plate after another and analyzing each almost instantly.
- In Arizona, the Maricopa County Sheriff’s Facial Recognition Unit, using a type of equipment prevalent in war zones, records 9,000 biometric digital mug shots a month.
- There are 96 million sets of fingerprints in Clarksburg, a volume that government officials view not as daunting but as an opportunity. This year for the first time, the FBI, the DHS and the Defense Department are able to search each other’s fingerprint databases, said Myra Gray, head of the Defense Department’s Biometrics Identity Management Agency, speaking to an industry group recently. “Hopefully in the not-too-distant future,” she said, “our relationship with these federal agencies - along with state and local agencies - will be completely symbiotic.”
- The effectiveness of this database depends, in fact, on collecting the identities of people who are not known criminals or terrorists - and on being able to quickly compile in-depth profiles of them. “If we want to get to the point where we connect the dots, the dots have to be there,” said Richard A. McFeely, special agent in charge of the FBI’s Baltimore office.
- Or, as most often happens, it could make no specific determination, which would mean that Suspicious Activity Report N03821 would sit in limbo for as long as five years, during which time many other pieces of information about the man photographing a boat on a Sunday morning could be added to his file: employment, financial and residential histories; multiple phone numbers; audio files; video from the dashboard-mounted camera in the police cruiser at the harbor where he took pictures; and anything else in government or commercial databases “that adds value,” as the FBI agent in charge of the database described it.
In Gaza, lives shaped by drones
by Scott Wilson
- Across northern Gaza, the response to the arrival of drones overhead is swift and, for some, almost involuntary. Their near-constant presence shapes life beneath them in a thousand ways — from how Islamist militants communicate to the color of exercise clothes chosen for a morning jog to the quality of satellite-television reception. When the buzz begins, an unemployed tailor in the hilltop village of Ezret Abed Rabbo walks to his window and opens it — one, then another, until the glass in all of them is safe from what he expects to be an imminent blast. The most recent rocked the area in late October when Israel responded with drones and F-16s to the attack on Ashkelon, killing nine Palestinian militants. “For us, drones mean death,” said Hamdi Shaqqura, a deputy director of the human rights center. “When you hear drones, you hear death.”
- Tsach was part of a small group that created the first surveillance drone in the bitter aftermath of Israel’s 1973 war with Egypt and Syria, where early intelligence failures and battlefield setbacks gave way to a lesson-filled Israeli victory. Among those lessons was the danger posed to Israeli forces by a lack of real-time intelligence. Israel could not track Egypt’s mobile surface-to-air missile sites, leaving pilots and tank commanders with worthless days-old information on their locations. Tsach recalled a single searing day when Israel lost dozens of planes to anti-aircraft fire. Before the war was over, Tsach and his crew, working around the clock, had developed a remotely piloted decoy aircraft to draw enemy fire. Photos from the time show a group of shaggy scientists posing with a small red model aircraft, the decoy that would evolve into the drones of today. Among them was Abe Kerem, who later helped pioneer what became the armed Predator drone used by the United States.
- “They hear the sound and they hold their breath,” Ramadan said. The head of the Gaza Community Mental Health Program, Eyad Sarraj, said the drones’ noise is something “you can’t escape.” Whether intentional or not, Sarraj said their constant presence induces a sense of helplessness among Gaza’s residents. “In the back of the minds of everyone here is fear — from the psychiatrist to the student, a sense that something terrible is going to happen,” Sarraj said. “The drones are part of that story. They are part of the conditioning — every time we hear them, we go back to those events of violence and death.”
- His customers still make for the doors at the first telltale signs the picture is fraying, as it did during a recent Chelsea and Liverpool match. For reasons that no one can explain, only Russia Today, an English-language channel promoting Russian views, is resilient enough to survive the drone interference. “The problem is in the sky,” said Nahed Hammad, who sells satellite dishes from his dimly lit storefront a few doors down, “not in the receiver.”
This blog post is full of links.
#dwellingThings I Have Written Elsewhere #1322690400
This is a piece titled Airport Timer
which was originally published in November 2011 on the Near Future Laboratory weblog.
There's a passage in David Pascoe's book Aircraft
where he talks about how none of the airports of the time were prepared for the introduction of the 747. Specifically there was no part of the physical infrastructure of an airport that wasn't overwhelmed by the size of and volume of the "jumbo" jet.
None of the waiting areas were large enough to accommodate the number of passengers getting on or off the planes. Often the planes themselves were too big to fit in the loading bays outside the terminals and the few enclosed jetways that had been in use up to that point were too small to even reach the doors on the planes.
Later in the book he goes on to describe a similar clusterfuck ushered in by the hostage taking during the 1972 Munich Olympics and the decision to install security checkpoints and passenger screening areas in airports. The just opened Dallas/Fort Worth airport was particularly hard hit. Although its design was modular and extensible from the outset (with all the terminals as simple semi-circles that could be snapped together like Lego up to the 10 miles in length) the buildings themselves were too narrow to retain any design or aesthetic after they been cut in two by x-ray machines and the lint trap of people waiting to go through them.
I was thinking about this last month when I had the misfortune of flying out of Terminal 7 at New York's JFK airport. Architecturally, Terminal 7 resembles two staggered butter sticks. The first butter stick is where you check in and is connected to the second "stick" which houses the departure gates by a short flight of stairs. In between the two, just in front of the stairs, is where you go through airport security.
United Airlines flies out of Terminal 7 so at least some of the misery of the security process can be blamed on United poisoning any and everything it comes in to contact with. The rest, though, is a combination of the need for the Transport and Security Administration (and their international counterparts) to indulge itself in ever greater security theater of Broadway musical proportions; the inability of people to imagine any kind of personal efficiency or shared responsibility getting through the line; and a New York City scale "Fuck you, never again" attitude to the process born out of the reality of the 9/11 attacks. All multiplied by the ever increasing numbers of people flying to and from, and especially to and from New York City.
There isn't much to say about the other terminals at JFK. Both Terminal 4 and the newer addition to Terminal 5 are little more than oversized cargo ship containers with drywall and designer handbag shops but at least they are big enough to dampen the indignity of the fear and paranoia that define contemporary air travel. Put another way: Terminal 7 is just too small and the security line is where everything grinds to a simultaneously depressing and rage-inducing halt and forces everyone to in to a shared despairing for all humanity, all the while with too little space to comfortably take off your shoes.
So I made a website: http://airport-timer.spum.org
Airport Timer is a simple web-based stopwatch application to record how long it takes to get through security at the airport.
Before you get in the screening line you enter, by hand, the three-letter airport code and the name of the terminal you're in and then press the start button which launches a timer in the background. Then you put your phone (presumably) back in your pocket before you are disappeared for spooking the security agents. When you make it through to the other side you press the stop button which stops the timer and, after a confirmation screen, uploads the airport code, the terminal and the time you spent (measured in seconds) going through security to Pachube. There's also an option to send a pithy message to Twitter.
That's it.
The site uses the Twitter API as a single-sign-on provider but that's mostly as a kind of half-assed throttle on the API that proxies and sends the timing data up to Pachube. Because of the way that the Twitter kids have built their Javascript widgets and because there's currently no place to store the Twitter user associated with a given report in Pachube there's a reasonable argument that you shouldn't need to log in at all. Modulo the part where even Instapaper gave in and forced people to create user accounts on the site. Anyway, you need to log in with your Twitter account.
The sites also uses Pachube as a datastore because it seemed like an obvious place to test the claim, in a networked world, that "every human is a sensor". Pachube's data model consists of three nested pieces: Environments (airports), Data Streams (terminals) and Data Points (individual time through security reports). The first two can be assigned additional metadata (tags, location, etc.) but the data points can only contain a timestamp and a value.
Which makes sense but right away the inability to add metadata to individual data points means that I can't record who just went through security or generate, easily, the "your stuff" style personal reports that people expect from social websites. Arguably Pachube is not a social site except for the part where, in a world where we are all sensors, any centralized time-series service that has humans as inputs will be measured on its ability to abstract the data. Robots may not care (or need) to see all that information bucketed by airport or by Wednesday versus Tuesday but we do.
You could just as easily write a backend for this kind of site using MySQL or Solr. Solr's ability to facet by date and eventually to do nested faceting (for example, to facet by airport and then for each airport by week or to facet by user and then by airport) makes it an attractive possibility but I'm choosing to use Pachube because it is a logical meeting of minds.
There are no "report" style pages for individuals or airports yet. There's actually a lot of stuff the site doesn't do yet. It does not try to retrieve your GPS coordinates automatically or use them to auto-detect your airport or validate that you're really at Charles de Gaulle aiport and not sitting at a coffee shop in Winnipeg. It does not have a magic auto-completing list of terminals for each airport. It does not (and will never) have heat maps.
Some of these things will come with time. I have already imported all of the whereonearth-airport data in to a Solr instance so auto-detection and validation are both more than theoretically possible. Auto-complete for terminals is little more wrapper code around the Pachube API to pull out the titles of terminals (datastreams) for a given airport (environment/feed). But for now, it's just a simple thing to record the data and put it somewhere safe and public.
This blog post is full of links.
#timer